Up to a few years ago, security at arenas and stadiums mainly consisted of physical gates, bag checks, and crowd management. Now sports and entertainment venues resemble microcities, technologically built to heighten onsite and external experiences. From the ubiquitous Wi-Fi to systems that control the lights, video, and HVAC, every part of these venues are linked through digital networks.
While this interconnectivity helps create incredible live and remote experiences, it also opens the door to cyber events. Unlike on-site threats to venues in the past, threat actors don’t even need to be in the same country to steal credit card data, disrupt broadcasts, or shut down an event.1 For venue owners and operators, mitigating these risks is a core part of keeping fans safe and protecting their bottom lines.
The Modern Arena Vulnerabilities
Cyber events against sports and entertainment industries have escalated over the past several years. These arenas are an attractive, high-profile target, and threat actors are hitting them with a range of cyber events, including ransomware, data breachers, and business interruption.2 It’s not just large arenas in the crosshairs, cyber events have targeted a variety of smaller venues as well, such as zoos, concert halls, and racetracks. A venue’s interdependent network and the public’s demand for connectivity and entertainment, underscores the need for robust cybersecurity measures and risk management strategies for venues of all sizes.
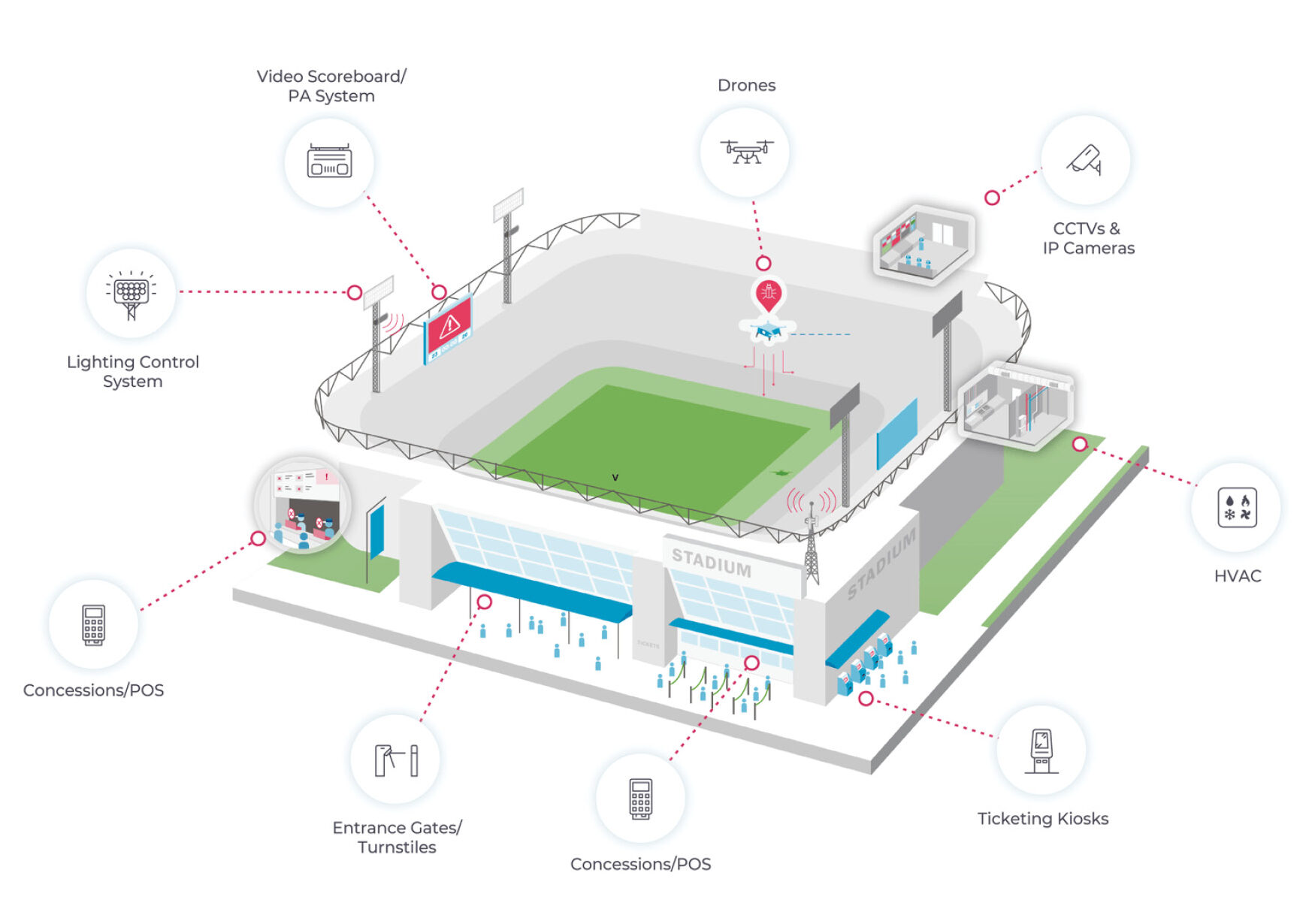
Sports and entertainment venues rely on several networks to create a live, ‘smart’ experience. This connectivity also provides a large attack surface for bad actors to gain access.
- Operational Technology (OT): The systems that run the building, with vulnerabilities such as lighting controls and scoreboards.
- Fan-Facing Tech: Public Wi-Fi is always a target. Hackers set up fake Wi-Fi networks (Evil Twin hotspots) that mimic a venue network to steal data or redirect users to malicious websites.
- Ticketing: A multi-system vulnerability, ticketing involves third-party vendors and venue management networks. Attackers on ticketing systems have caused significant financial losses, such as the December 2022 attack that shut down the Metropolitan Opera’s ticket office, during a season when the venue sells $200,000 of tickets every day.3
- Venue Access: Attacks that affect egress can create crowd control issues. Denial of entrance can create confusion and delays, while denying exit from an event can create potential panic.
- Point-of-Sale (POS) Systems: Onsite sales of food and merchandise are a valuable financial opportunity for venues, teams, artists, and attackers.
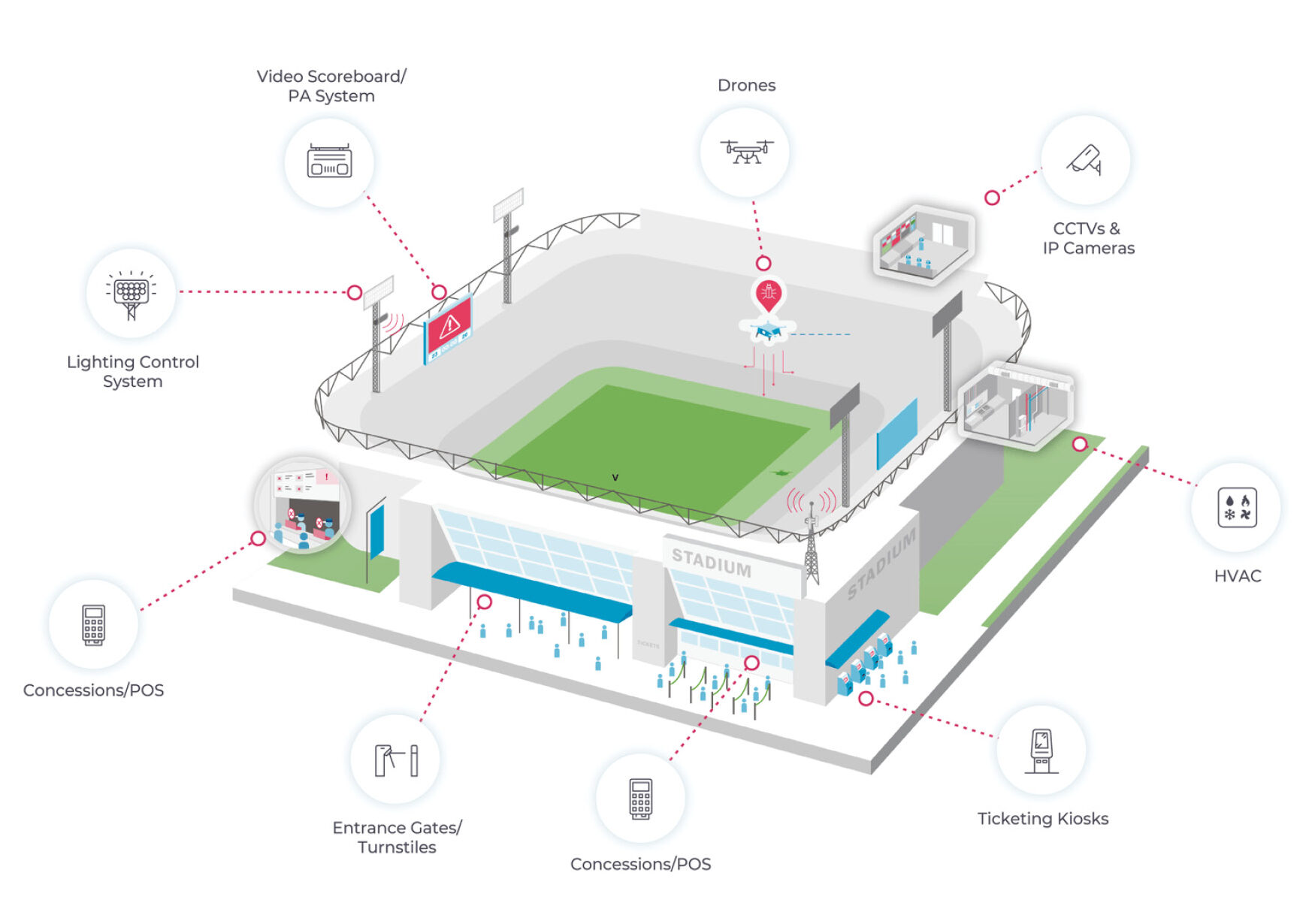
Source: OT & IoT Cybersecurity for Stadiums & Arenas. Nozomi Networks.4
Vendors May Be a Weak Link
Most major events are a complex ecosystem of contractors, sponsors, and third-party vendors. Research shows that 75% of third-party breaches target the technology supply chain.5
As best as possible, venues should verify all third-party networks are secure, as a breech in a vendor’s system can be used to penetrate a venue’s firewalls. In 2024, a massive data breach at Ticketmaster occurred after an attacker gained access to a cloud database using stolen credentials from a third-party vendor. In this single breach, the attackers claimed to have stolen 1.6 terabytes personal information from 560 million customers, including names, full credit card information, phone numbers, and personal and email addresses.6
Protecting Physical Risks
Cybersecurity should protect more than digital systems connecting data and information, it should also address physical liabilities. The cyber-physical threat is why organizations like CISA categorize stadiums as critical infrastructure. When a system breach can stop an elevator, turn off HVAC systems, deny egress, an attack becomes a public safety concern.7
During the 2018 Pyeongchang Winter Olympics, malware known as ‘Olympic Destroyer’ wiped out data on servers right before the opening ceremony. Attackers not only stole data they also paralyzed the official app, disabled the Wi-Fi, and shut down automated ski lifts.8 With several high profile, worldwide events scheduled in 2026, the Pyeongchang attack illustrates why disrupting such events has allure for threat actors.
Third-party attacks are not only targeting technology stacks but also critical infrastructure such as energy grids, HVAC systems, and water supply systems. Unlike an IT breach, in which the object is data theft, an OT breach can lead to real-world, physical damage with devastating public health and safety consequences.9
Is Traditional Insurance Enough?
Venue owners and operators may assume their current
insurance will cover a cyber event. However, traditional
policies often are inadequately able to cover the wide range
of risks a venue faces, or, as coverage evolves, policies
may be out-of-date. Sports and entertainment venues and
organizations require multiple lines of coverage, necessitating
careful consideration and evaluation of potential coverage
gaps for cybersecurity or data privacy claims.
- Commercial General Liability (CGL): These policies usually only pay out if there is physical property damage or bodily injury. CGL policies are beginning to exclude cyber incidents.
- Property Insurance: Standard business interruption (BI) coverage is often triggered by physical loss (like a fire). If a threat actor attacks a venue’s POS systems that shuts merchandise sales, property BI might not cover lost sales.
- Biometric Data: Many stadiums now use facial recognition or fingerprints for entry. In 2024, a class-action lawsuit was filed against the New York Mets, alleging the organization violated biometric data privacy laws.10 Many cyber policies exclude the unauthorized collection of biometric data, leaving the venue to pay for costs out of pocket.
- Crime: While crime coverage covers financial theft, it often excludes many of the attack vectors associated with cybercrimes. Social engineering may be endorsed, but carriers often cap coverage and limits.
Building a Digital Defense
Cyber protection for venues starts by implementing a proactive, risk mitigation strategy.11
- Network Segmentation: Keep guest Wi-Fi separate from operational networks, such as lighting, HVAC, and ticketing. If a threat actor accesses one network, they shouldn’t be able to access others.
- Rigorous Patch Management: Maintain constant software release oversight, updating patches and fixing vulnerabilities in every system.
- Employee Training: Staff is the first line of defense. Most ransomware attacks start with a phishing email. Conduct regular training to educate employees to spot scams and report suspicious activity
- Incident Response Plans: Just like plans for a fire or a medical emergency, a cyber event response plan details communication with fans, legal teams, and law enforcement.12
The Bottom Line
In the world of sports and entertainment, the financial costs of a cyber event can be staggering. Cyber events on sports and entertainment venues can expose personal and venue data, endanger fans’ physical safety and venue infrastructure. Safeguarding venues, organizations, and fans is a critical security concern that requires a proactive and comprehensive risk mitigation strategy.
In today’s risk environment, cyber insurance complements cyber controls.13 Together, they build a defense to protect organizations from cyber events, and a financial backstop for the losses that follow.